IT security for the healthcare sector
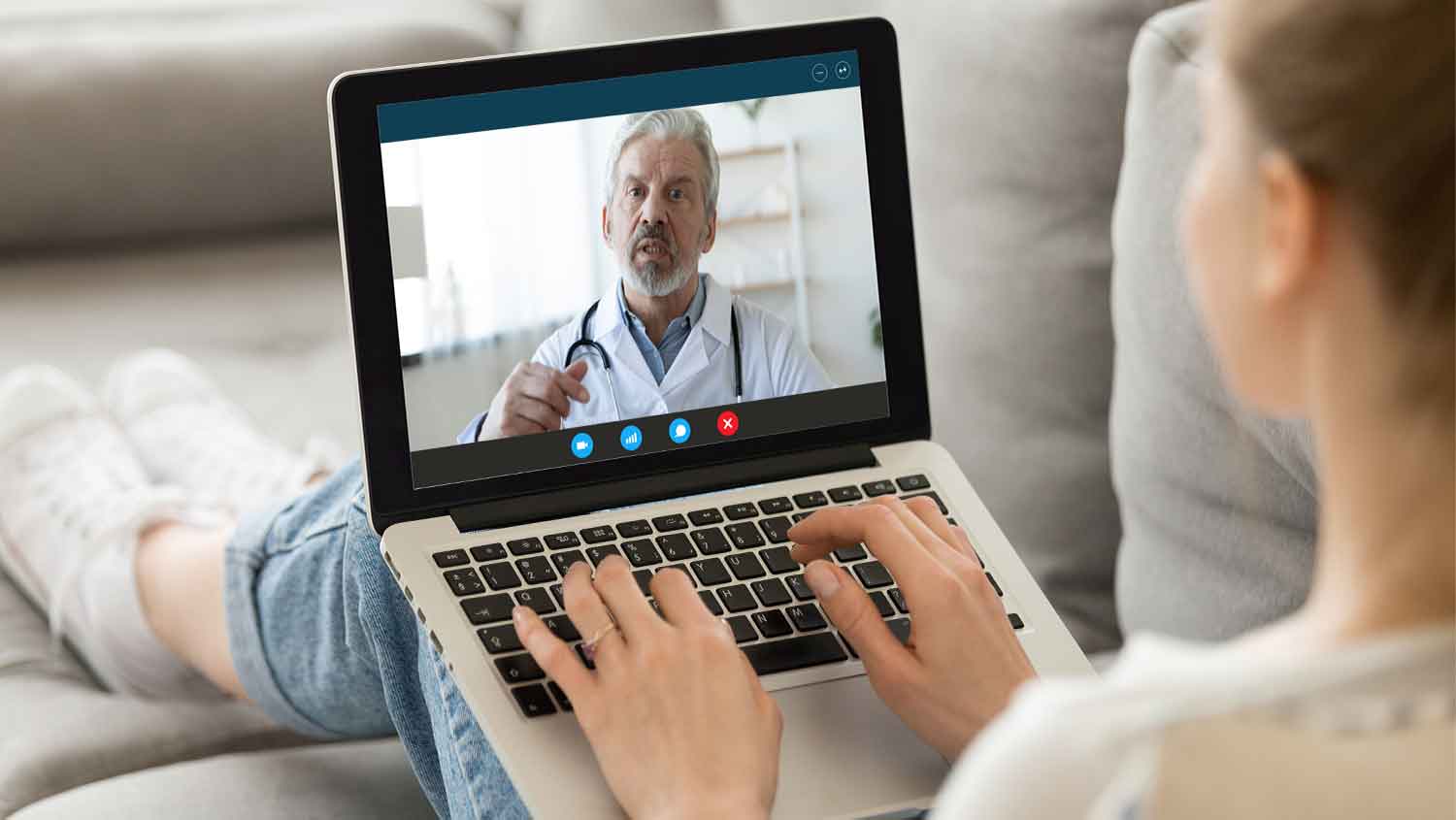
The process of digitization has accelerated in the wake of the pandemic as well as under the “Krankenhaus Zukunftsgesetz” (KHZG). New digital applications and services have been introduced to meet the demand for telemedicine services.
Improved networking as a result of digitization establishes faster information transfer and thus more efficient processes for diagnostic procedures and treatments. For improved internal as well as external communication procedures, clinics are also turning to modern and networked cloud applications and Software as a Service.
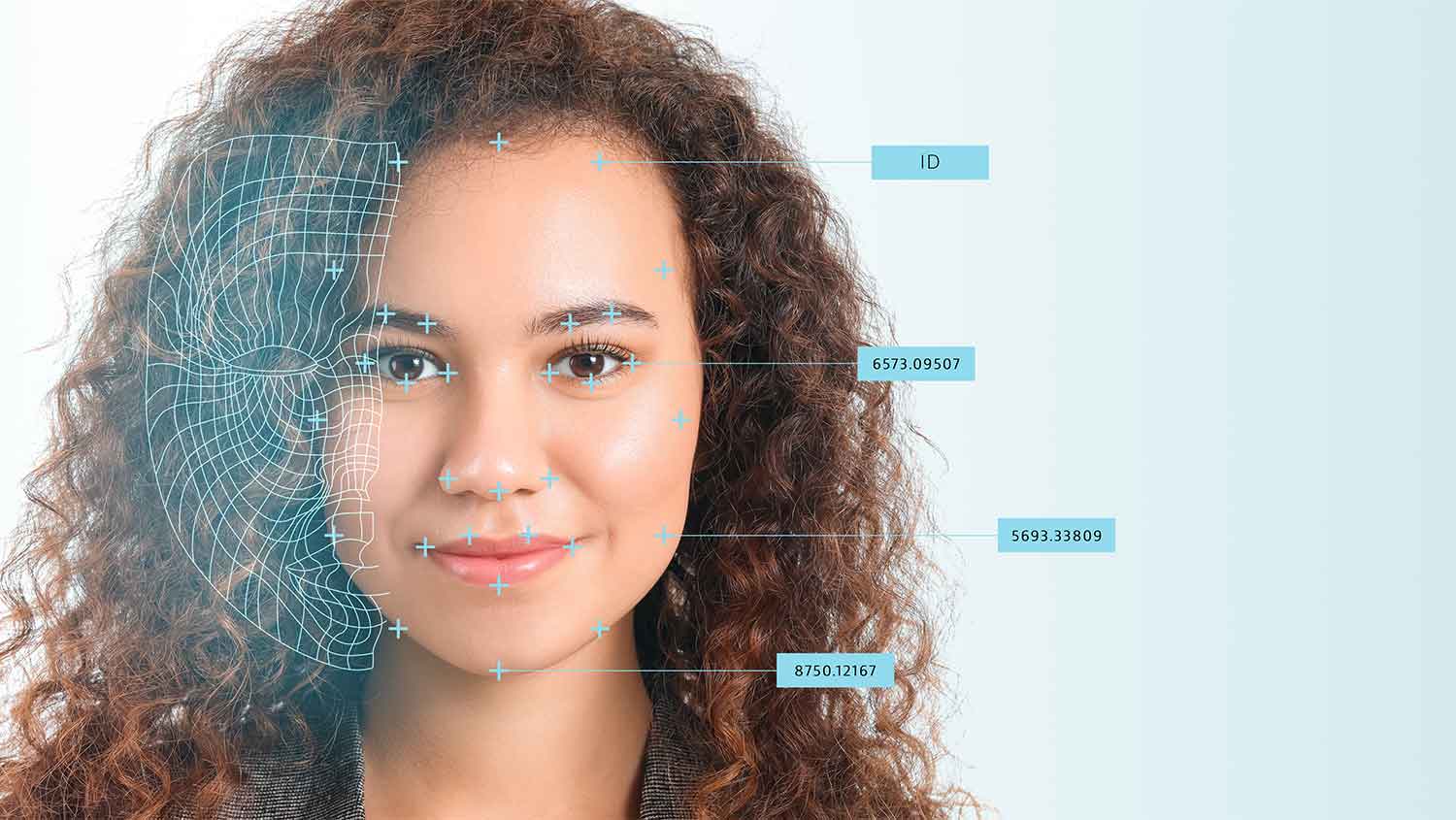
However, this rapid digitization is also making healthcare facilities more vulnerable to cyber-attacks, as the new digital capabilities are also creating new gateways for criminals to enter.






 HWS Gruppe
HWS Gruppe
