The consequences of phishing attacks for companies
Phishing attacks on companies are on the rise. You would think that everyone would be familiar with the term. In fact, a recent report from Proofpoint showed that many employees are unaware of what phishing actually is. And they are therefore unable to assess how they could be affected by it. And, ultimately, how they can protect themselves from such attacks.
That’s why we’d like to start by defining the term before going into what consequences this has for companies. And we show you what simple tools can help with prevention.
Where do we face phishing?
Phishing describes the process by which fraudsters attempt to obtain personal data using forged e-mails, instant messages, or websites. A special form is a so-called vishing, in which this fraudulent process is carried out via the telephone.
In the case of private individuals, the aim is usually to obtain payment and identity data or passwords directly. A variation is the (surreptitious) download of malware; whether in the form of ransomware to extort a ransom after data encryption or to form a so-called botnet. This ensures that the PC can be remotely controlled, whereby it can become the starting point of another wave of infections, for example.
In the business environment, phishing attacks do not necessarily primarily target the individual concerned. Often, the entire company is at the center of such attacks. Even if companies still have weaknesses in their technical security, the phishing phenomenon shows that people are the most fragile link in the security chain. This is because people are targeted using mailings or telephone campaigns to elicit relevant information from them. Employee awareness training repeatedly shows how carelessly employees pass on information or follow (dubious) links during good social engineering campaigns.
For a large-scale social engineering campaign against a specific company, tapping user and access data can certainly be the first step. Often, however, the actual attack is preceded by espionage attempts. Perpetrators use fictitious e-mails and/or phone calls to specifically identify people responsible for the finance or IT departments, for example. This enables them to launch the actual attack on the company at the right point. These targeted attacks on the upper management level are often more successful than an untargeted attack on individual employees since a broad information base is available here; built up via external as well as internal sources.
Possible campaigns on companies
Possible campaigns based on lucrative profits alone are the focus of phishing attacks. Small and medium-sized companies and large hidden champions are particularly often targeted by fraudsters. Because of their low profile, they often lull themselves into a false sense of security and neglect the protection of their networks and systems. This is a fatal mistake. Since weak security systems and access restrictions, as well as a lack of investment in employee awareness and training, can be very costly.
One form of social engineering campaign that has become increasingly common is CEO fraud, also known as business email compromise. In this case, e-mails are sent to employees in the name of superiors up to the top management level to obtain their data. At the same time, however, executives, in particular, are also targeted by cybercriminals.
In addition to such targeted campaigns, attackers also continue to use classic methods, such as fake links or attachments to supposedly download business-relevant documents. Especially in the business environment, where there is a compulsion to open files or follow up on information, attackers have an easy game if they target relevant topics.
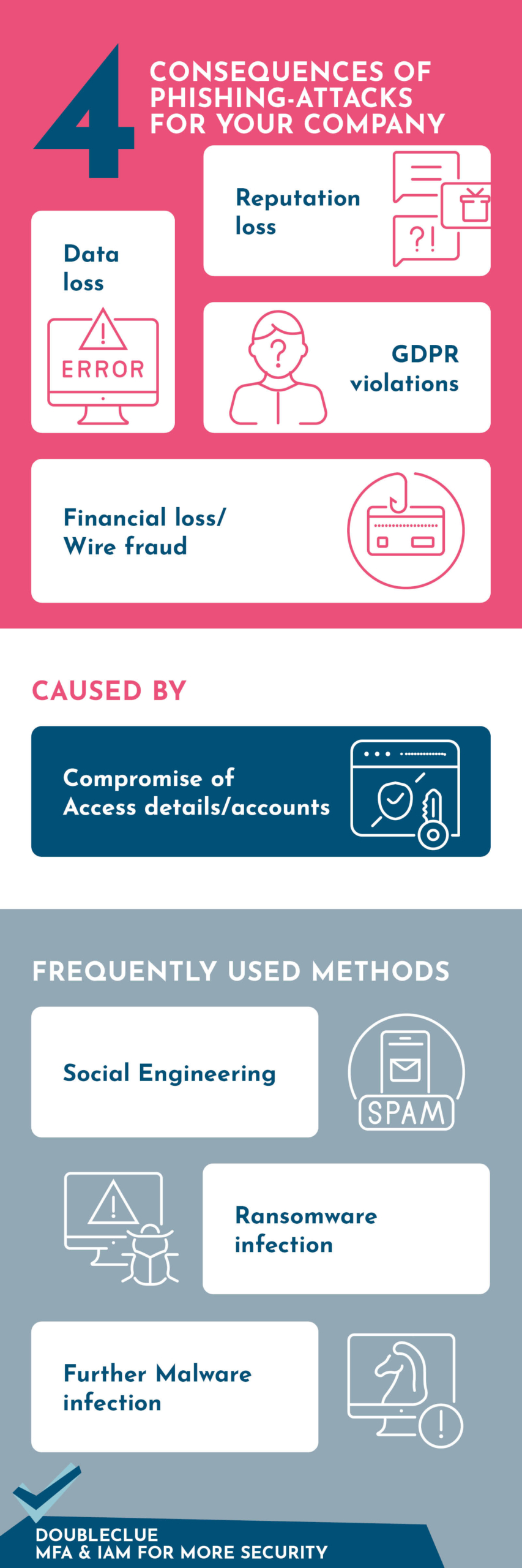
The consequences for companies
A successful phishing attack can cause several major problems for businesses. We have summarized the most common consequences and causes in the graphic.
Well protected thanks to MFA and IAM
When dealing with phishing, it is essential to particularly safeguard the human factor. Even the best firewall or the latest anti-virus program is of no use if an employee – on the phone or in a fake e-mail link –reveals company information or access data. At least you can protect yourself and your company against the latter using sensible identity and access management and MFA (multifactor authentication).
One example of such software is DoubleClue, which combines both. Find out more about all the benefits of using DoubleClue here.
 HWS Gruppe
HWS Gruppe


